Our Comprehensive Services
Author: FUSION 1
Shifting tactics fuel surge in business email compromise
In response to how FUSION 1 IT SOLUTIONS can help, exploring the shifting tactics of cybercriminals in business email compromise attacks is crucial. The article 'Shifting tactics fuel surge in business email compromise' offers valuable insights into these threats and outlines three steps you can take to ...
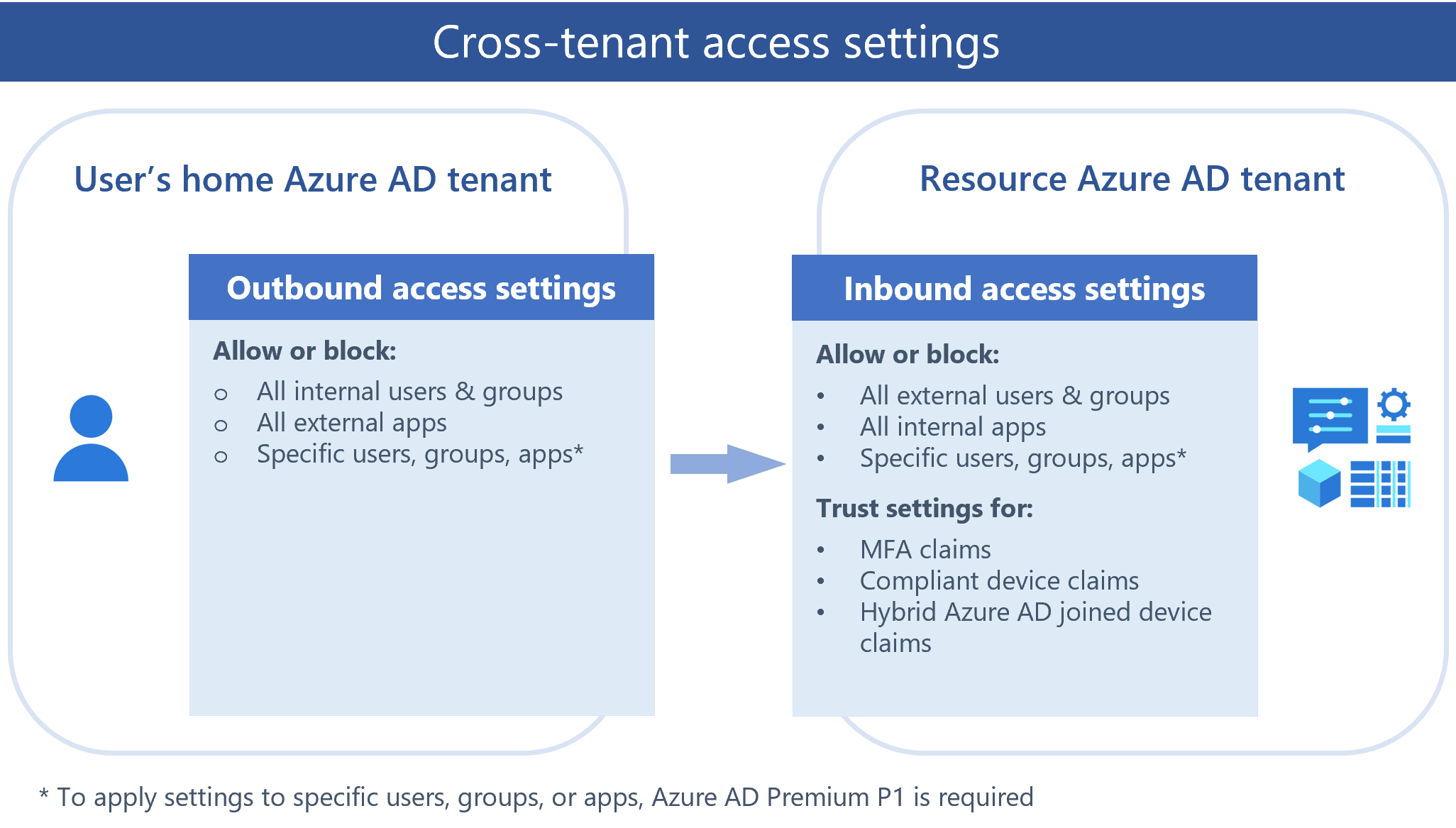
Cross-tenant access with Azure AD External Identities
Azure AD (Active Directory) is a cloud-based identity and access management service within Microsoft Azure, designed to help you manage user and device identities while controlling access to resources. One of its key features is cross-tenant collaboration, which allows users from different organizations to seamlessly collaborate and ...
The Ultimate 2025 New Year’s Resolutions For Tech Leaders
As cyber threats evolve, organizations must adapt to the increased demands of safeguarding systems while embracing AI and cloud technologies. FUSION 1 can assist tech leaders in navigating these challenges with strategies designed to reshape security efforts and enhance organizational success.
Read More...
Many Businesses Are Nearing the Completion of Their Cloud Migrations
Within the next three years, many organizations will be running most applications on public clouds, according to new research. This shift presents an opportunity to reshape your operations with FUSION 1.
Read More...
The Ultimate 2025 New Year’s Resolutions For Tech Leaders
As cyber threats evolve, organizations must adapt to the increased demands of safeguarding systems while embracing AI and cloud technologies. FUSION 1 can assist tech leaders in navigating these challenges with strategies designed to reshape security efforts and enhance organizational success.
Read More...
Happy Holidays!
Wishing you and yours a happy holiday season from FUSION 1 IT SOLUTIONS!
Building a Holistic Insider Risk Management Program
The risk landscape has evolved significantly with the expansion of digital technology. The amount of data generated is projected to exceed 180 zettabytes shortly. Given this shift, traditional methods of identifying and addressing risks are often insufficient. While many organizations have focused on external threats, risks originating ...
Add Azure Active Directory (Azure AD) as an identity provider for External Identities
You can add Azure Active Directory as an identity provider option for B2B collaboration. If an external guest user has an Azure AD account through work or school, they can easily redeem your B2B collaboration invitations or complete the sign-up user flows using their Azure AD account. ...
CISOs list human error as their top cybersecurity risk
Three in four CISOs identify human error as their top cybersecurity risk. Prioritizing security awareness education and implementing guardrails to reduce employee errors are fundamental steps in reshaping your cybersecurity strategy.
Read More...
The power of purpose-built cloud infrastructure
As businesses seek tailored solutions, the cookie-cutter cloud model is becoming less effective. Purpose-built cloud infrastructure, customized to handle specific workloads, provides low latency, high throughput, and greater resource utilization. With FUSION 1's expertise, you can leverage these benefits to meet your unique requirements.
Read More...